Mitigating a 3 Gp/s UDP Carpet Bomb Attack
How RoyaleHosting automatically mitigated a 3 Gp/s UDP carpet bomb DDoS attack targeting a customer subnet, demonstrating advanced network protection and automated edge filtering capabilities.
In mid-September, RoyaleHosting mitigated a 3 Gp/s distributed denial-of-service (DDoS) attack that targeted a customer subnet. The incident illustrates a trend we’re seeing more often: attackers combining volumetric traffic with strategies meant to stress mitigation systems and spread impact across many addresses.
Attack characteristics
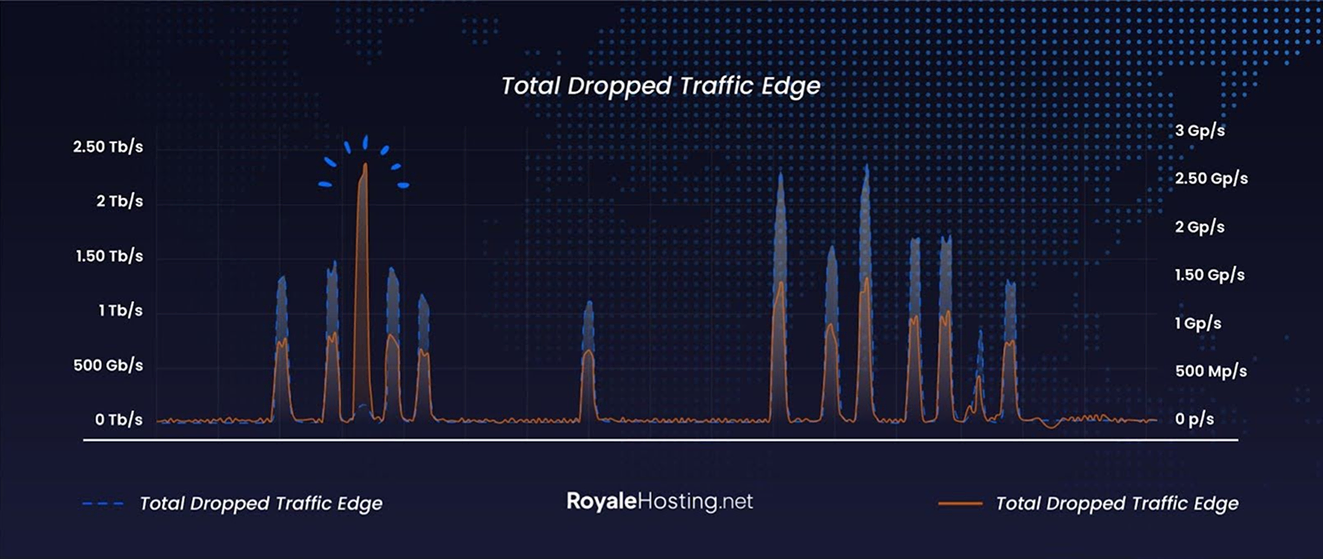
The attack was UDP-based and took the form of a carpet bomb, targeting every IP within the customer subnet rather than a single host. That distribution increases the complexity of mitigation because the packet rate is spread broadly across many endpoints, making it harder to separate malicious flows from legitimate ones at the per-IP level.
Although the event included volumetric elements, discussing TB/s numbers isn’t necessary here. The operational challenge was the distributed hit on the subnet and the sustained pressure on packet-filtering and inspection resources.
How we mitigated it
RoyaleHosting’s edge systems detected the anomalous behavior and applied automated, network-wide filtering to drop malicious packets at the edge. The mitigation completed without requiring any manual intervention.
Once the attack was detected and automatically mitigated, our Network Operations Center (NOC) engineers received real-time alerts and began closely monitoring the event. While the automated systems handled the mitigation process without disruption, the team analyzed traffic patterns and mitigation behavior in real time to better understand the attack vector.
This hands-on monitoring provided valuable insight into how our defenses performed under sustained, distributed load. The event served as a practical stress test for our DDoS protection stack, confirming its resilience while also revealing opportunities for further optimization. Based on these observations, our engineers are implementing fine-tuned improvements to ensure even faster detection and enhanced filtering efficiency in the event of future, larger-scale attacks.
Why this matters
DDoS actors are increasingly optimizing to impact mitigation systems and leveraging large botnets to execute low and wide attacks that test the limits of filtering equipment. Successful defense requires automated detection, scalable edge filtering and the ability to apply targeted mitigations across a distributed attack surface. At RoyaleHosting we continue to invest in real-time detection and adaptive mitigation so customers remain protected against both high-volume floods and high-complexity attacks.